At WiseGEEK, we're committed to delivering accurate, trustworthy information. Our expert-authored content is rigorously fact-checked and sourced from credible authorities. Discover how we uphold the highest standards in providing you with reliable knowledge.
What are the Different Uses for RFID Technology?
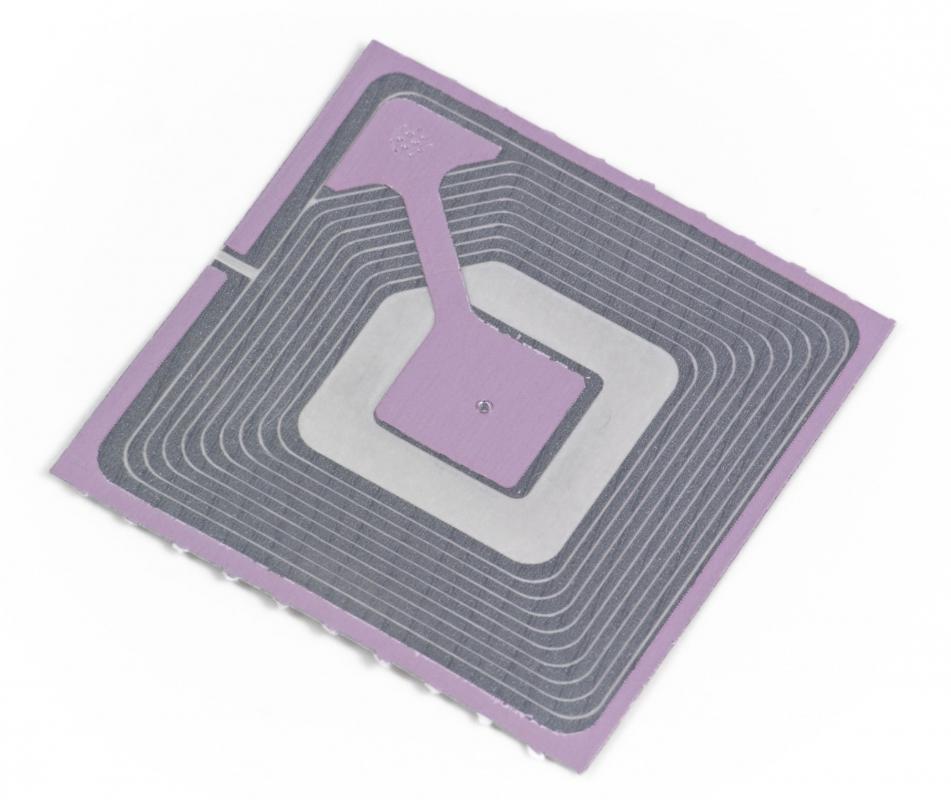
Radio frequency identification, or RFID, technology uses small embedded tags to store and transmit modest amounts of data. All RFID tags consist of an antenna and an attached microchip that stores and processes information. RFID tags are read by special readers, which can access and in some cases modify the information contained on that tag’s microchip. RFID technology is extremely useful in any application that requires monitoring and tracking discrete items or individuals; RFID tags have been used in inventory management and control, human and animal identification and monitoring, and to facilitate financial transactions in place of cash or credit.
RFID technology is widely used in inventory tracking. RFID tags are included either in individual products or in pallets or groups of products. These tags allow easy and automatic management of inventory and supply, as readers can be used to determine the contents of a warehouse or trailer. Inventory tags often also include source, destination, and other key product information, all of which can be accessed instantly with tag readers. This allows corporations to streamline their supply chains, and also allows for easier back-tracking of shipments as needed.

In addition to allowing firms to manage inventory and transport, RFID technology can be used to prevent theft. Theft along the supply chain can be minimized by ensuring that a central database contains records for each stage of a product’s transport history. Tags embedded in individual products allow for excellent in-store inventory management and can effectively prevent theft as well.

Humans and animals can be tracked and monitored with RFID technology just as easily as packages and crates. In some cases, RFID tags can be implanted, generally to allow for the tracking of animals of scientific interest, children, or pets. Modern passports often employ RFID tags and can be scanned remotely by customs officials. Some concerns have been raised that information can be stolen from these passport tags.

The ability of RFID technology to easily and rapidly identify individual people or vehicles has led to its widespread use in many commercial systems. Combination tag-reader devices for cell phones can be used to query product tags or conduct transactions when the necessary infrastructure is in place. Many highway and public transportation systems already rely on RFID technology to handle payments. Cards or automatic transponders are linked to master accounts in a central database, and these systems can track the movements of people and vehicles, and debit accounts appropriately. These systems, much like passport tags, present some security risks.
AS FEATURED ON:
AS FEATURED ON:











Discussion Comments
How do you disable, disarm, or scramble these microchips?
Post your comments